If you’re a manufacturer, you’re considered highly vulnerable to security compromise, with 48% having experienced some kind of cybersecurity incident.
This makes it essential for manufacturers to prepare for CMMC—especially closing the gaps in their company’s digital assets, such as intellectual property and controlled unclassified information (CUI).
Manufacturers have increased their attack surfaces by deploying IoT devices, adding access points through remote employees, and expanding opportunities through unsecured supply chains.
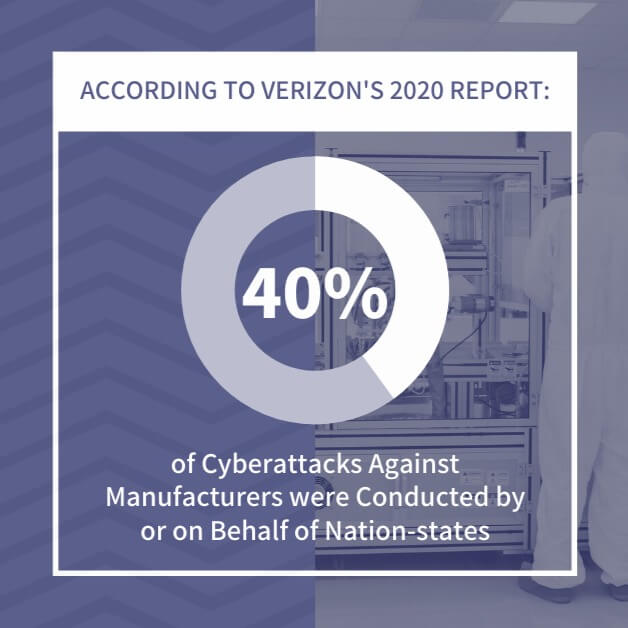
According to Verizon’s 2020 report, almost 40% of cyberattacks against manufacturers were conducted by or on behalf of nation-states.
Although some countries may not directly participate in cyber espionage, they do not enforce protections against the theft of intellectual property. For example, the United States and China have a long-standing dispute over violations of intellectual property law by Chinese businesses.
As Chris Golden, a former member of the CMMC Accreditation Body, put it:
“We’re losing a lot of intellectual property as a country to our adversaries through gaps in cybersecurity practices and maturity throughout the supply chain. And right now, that’s focused on DoD supply chain.”
What’s Considered Intellectual Property?
In the broadest sense, intellectual property (IP) refers to creations of the mind.
These creations may be copyrighted or patented works, but they may also be concepts and processes. They can be proprietary applications or devices, even if only for internal use.
IP is the idea that differentiates similar products or the way of executing a process that produces a unique result.
Copyright, patents, trademarks, and trade secrets are four specific types of intellectual property, but proprietary methods of operation are intellectual property as well.
Protecting IP ensures competitive advantage. As a manufacturer, you spend years taking a product from conception to market and devote hundreds of thousands of dollars in research and development to make an idea a reality.
When those efforts are not protected, you run the risk of a competitor taking that information and using it to develop a similar solution, erasing any competitive advantage you may have had. Even failed attempts can have intellectual value.
Steps You Can Take Right Now to Prepare for CMMC and Protect Your IP
Controlled unclassified information (CUI), like intellectual property, needs to be protected from security compromises.
This is why the DoD published its Cybersecurity Maturity Model Certification (CMMC) and is requiring compliance to CMMC standards for many companies in 2021. The phased model is designed to help government contractors build secured infrastructures to protect CUI.
These same measures can and should be used to protect IP.
A cybersecurity maturity model lets government contractors grow into a comprehensive security framework. This approach allows a company to spread the cost over time while ensuring a basic level of security across the enterprise.
The following areas or domains reflect the requirements of DoD’s CMMC, which outlines an excellent framework for protecting both CUI and intellectual property. If you prepare for CMMC by implementing these guidelines, you can strengthen cybersecurity in your manufacturing.
1. Assess Security Risks
Before implementing changes, you need to assess your current security risks. That means looking at your entire organization, its digital assets, and personnel to determine what impact a compromise would have on operations, reputation, and financial stability.
Scanning for vulnerabilities should be the first step in any risk assessment. Scans provide a list of weaknesses that can then be prioritized and mitigated. The effort should include both vendor-supported and non-vendor-supported products as well as supply chain vendors.
Once the risks are identified, you should prioritize the risks and establish mitigation plans to be put into place. Periodic risk assessments should be performed to identify additional vulnerabilities that could place your business at risk.
2. Control Access
Limiting who can access what is an important step in preventing and containing security incidents. By restricting what an end-user can access limits, the damage hackers can do if they do compromise a system is limited. Here is a list of practices to follow to control user access and prepare for CMMC certification:
- Restrict access using a least-privilege model. For example, an employee needs to access proprietary information such as sales volumes for a special project. Instead of granting full access to the data, give the employee temporary permission that expires in 30 days.
- Limit what functions can be performed by an end-user, including other computer systems. Not all applications need to read and write to databases or files. Controlling what a person or application can do with data minimizes the risk of unwanted duplication of information.
- Control connections to and from external systems and limit the information available on publicly accessible systems.
- Restrict the number of portable network-accessible storage devices, wireless access points, and edge devices.
- Monitor remote access and route traffic through an established control point.
- Deny access after a preset number of unsuccessful login attempts and terminate sessions after periods of inactivity.
Limiting access is the best way to secure data– If hackers can’t get to it, they can’t steal it. Other controls may include encrypting IP and CUI data while in transit or at rest.
3. Audit System Activity
The only way to know what is happening in cyberspace is to track it. And that also means logging.
You should use audit trails to monitor, analyze, and investigate unauthorized system activities, including logon attempts. A network should ensure that individual user activity can be traced back to the originator, and all audit records should be date-and-time stamped.
Managing the volume of data can be overwhelming without the use of automated tools. There are tools available to help you:
- Review and analyze logs – These tools can evaluate information and report anomalies for evaluation.
- Monitor logging function – If an application or service stops logging, an alert can be sent.
- Transfer logs to a central location – Logs should be maintained in a central location for easier access.
- Restrict user access – These limit the individuals who can access the logs, and specifically those who can modify and delete files.
Audit trails are the only way to confirm unlawful or unauthorized activity. The logs should be well-protected from internal and external threats.
4. Train Staff
People are the weakest link in any cybersecurity effort. Verizon’s recent report on data breaches found that close to 95% of data breaches are the result of human error.
It’s not that people ignore security; they just become focused on their job responsibilities and meeting deadlines. In their rush to get things done, they click on a link they shouldn’t or respond to an email without thinking.
Keeping employees aware of possible threats is essential to any cybersecurity program. Everyone from the CEO down should understand how their actions can put the company at risk.
Periodic reminders and awareness training can keep staff informed on what to look for. Consider simulating threat scenarios to reinforce training. Gamification of cybersecurity awareness can have a positive impact on end-user awareness and participation.
5. Authenticate Users
Users are not just people. Users can be applications, processes, or devices that are acting on behalf of people.
IT departments need to identify and authenticate anyone or anything trying to access the network. User identifiers and passwords are the most common types of credentials used to authenticate users. Best practices for the use of user IDs and passwords include:
- Establish a minimal level of complexity
- Prohibit password reuse
- Require an immediate change of password after a temporary password is used
- Encrypt passwords while in transit and at rest
Cybersecurity departments should consider multi-factor authentication (MFA) for identification and authentication. Alternatively, they can implement a zero-trust environment that assumes that all users cannot be trusted whether they reside behind the firewall or not.
6. Maintain Systems
Maintaining organizational systems is an essential part of any cybersecurity program, yet it is one that is often overlooked.
Updates include patches and fixes, but they also include changes to protect against possible vulnerabilities. If the updates are not applied, those weaknesses remain open to attack.
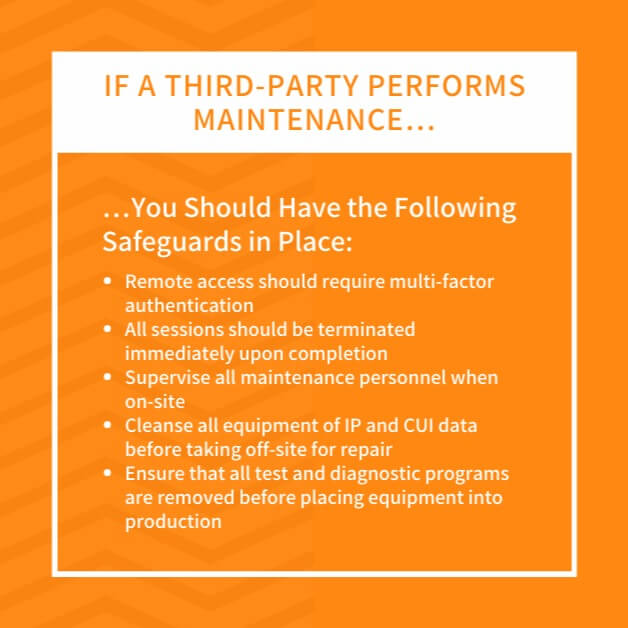
If a third party performs maintenance, you should have the following safeguards in place:
- Remote access should require multi-factor authentication
- All sessions should be terminated immediately upon completion
- Supervise all maintenance personnel when on-site
- Cleanse all equipment of IP and CUI data before taking off-site for repair
- Ensure that all test and diagnostic programs are removed before placing equipment into production
Working with the same vendors for long periods of time makes it easy to forget that they aren’t part of the team. Your company may have a long-standing relationship with the vendor, but it doesn’t have the same arrangement with every employee.
7. Manage Media
Data is stored on a variety of media. It isn’t just on servers– It can be on external storage devices or flash drives. It’s essential that the following best practices be used when working with IP and CUI stored on media.
- Sanitize or destroy system media when it’s no longer needed
- Control and store system media in a secured physical facility
- Limit access to the storage facility
- Restrict the use of removable media as much as possible
- Prohibit the use of portable storage devices unless company-approved
- Encrypt storage of media to protect data
If using tape backups, IT administrators need to ensure that the backups are stored in a secure location with audited access control.
8. Manage People
As an employer, you should have procedures in place for managing access to restricted information during the hiring and onboarding process. These procedures should include practices for protecting IP and CUI when employees are terminated or transferred.
For example, when provisioning a new workstation, the default settings should be set for least privilege. Once new hires have finished onboarding, their supervisors can request the necessary access.
A clear process must also be in place for removing access to CUI and IP once an employee is no longer working for the company. Part of the process should include checking all portable storage devices as well as local and remote devices. IT should be informed as soon as possible that an employee will be leaving.
9. Control Communication Systems
Communication systems are the pathways that IP and CUI travel. If the pathways are secure, it makes it more difficult for hackers to compromise a system.
Microsegmentation is one way to secure communication networks. Creating subnetworks restricts how freely a user (or hacker) can move within the system. Transversing from one subnet to another takes time which aids in detection.
Other actions that can facilitate control include:
- Prohibiting remote activation of devices
- Encrypting all system management sessions
- Isolating the network and users as much as possible to minimize coordinated compromises
- Evaluating in-house code and scripts for possible vulnerabilities
- Increasing protection at the boundaries and on the edge
- Enforcing port and protocol compliance
Carefully control configurations. Document what the configuration standards should be and periodically confirm that they are still active.
Because the network landscape can change so rapidly, modifications to configuration settings can be overlooked. That’s why it’s vital to monitor system configurations.
10. Test System Integrity
Testing is the only way to ensure system integrity. Whether it is penetration testing or vulnerability scans, IT needs to exercise its systems to provide protection.
Here are a few ways to efficiently test your systems:
- Use tools to look for and protect against malicious code
- Make sure test tools are updated to work with new releases
- Track unauthorized attempts
- Install spam protection
- Configure security alerts
- Scan all downloaded files in real-time
- Check for email forgeries and block suspicious emails
Constantly monitoring the system is the best way to become familiar with how a system behaves. Anomalies to the behavior can be highlighted and investigated before a compromise can occur.
The Value of CMMC for Manufacturing
Whether or not your business is required to get CMMC certification, the CMMC is an excellent framework to ensure intellectual property is protected. Reviewing a CMMC compliance checklist can give you an idea of where your cybersecurity currently stands, and what you can do to improve it.
And for those wanting to do business with the DoD, CMMC compliance is required. All government contracts will require applicants to be certified at a Level 1. In some instances, the level of certification may be higher.
The DoD appointed the CMMC Accreditation Body to oversee the implementation of the CMMC program. The body has created a CMMC Third-Party Assessor Organization (C3PAO) that is responsible for delivering an accreditation process for companies wanting to offer CMMC services.
Don’t Try To Prepare for CMMC Alone
Trying to understand and prepare for CMMC requirements can be overwhelming, even for companies with dedicated IT personnel.
Rather than wait for internal resources to get up to speed on the CMMC requirements, look into CMMC consulting firms that can help get your business on a path to CMMC certification.
Looking to prepare for CMMC Compliance? Check out our (ungated) CMMC Compliance Checklist.
While working to secure CUI and prepare for CMMC, you can make sure your intellectual property is thoroughly protected.