TL;DR: A recent FBI warning again brings attention to cyber threats like phishing, callback phishing, ransomware, and DDoS attacks that pose significant risks to professional services businesses. Learn about their impacts on your business and the role of network security monitoring in safeguarding operations and reputation. The discussion includes strategies for effective defense and prevention.
Network Security Monitoring: Protecting Your Business
Network security monitoring is a critical tool in protecting your network, spotting suspicious activities early, and responding swiftly to potential threats.
Take the healthcare sector, where data breaches can have dire consequences, the importance of network security monitoring is crystal clear.
With US healthcare institutions facing about 1,400 cyberattacks each week, it’s a strong reminder that data protection, and network security monitoring is a necessity.
In this post, we’ll get to the heart of what network security monitoring means for your business.
We’ll discuss the types of cyber threats you should be aware of and how network monitoring can be your first line of defense. It’s not just about protecting data; it’s about ensuring the continuity and reliability of your services.
Understanding the nature of these cyber threats is crucial for effective defense strategies. From sophisticated email schemes to attacks that cripple network functionality, the risks are diverse and significant.
What is Network Security Monitoring?
Network monitoring is monitoring a computer network for any failures to ensure continuous network performance and availability.
This involves using a system that collects and analyzes data from various parts of a network. The 6 key aspects of network monitoring include:
Performance Monitoring: Assessing the performance, and hardware such as routers, switches, servers, and other devices. Key performance indicators include bandwidth usage, packet loss, latency, and error rates.
Fault Monitoring: Detecting and reporting network faults or failures. This could include identifying broken links, malfunctioning hardware, or other issues that disrupt normal network operations.
Traffic Analysis: Examining the flow of network traffic to identify patterns, such as peak usage times, or potential security threats like unusual traffic patterns that might indicate a cyberattack.
Availability Monitoring: All parts of the network are operational and accessible. This includes monitoring the uptime of network components.
Security Monitoring: Keeping an eye on network security by detecting suspicious activities that could indicate a security breach.
Configuration Management: Monitoring changes in network configuration to prevent unauthorized changes.
Network monitoring tools and software are used for these purposes, providing real-time alerts and detailed reports to network administrators.
This helps in proactive management, ensuring that any potential issues are resolved quickly to minimize downtime and maintain efficient network operations.
Common Threats Network Monitoring Protects Against
Phishing Attacks
Traditional phishing attacks involve deceiving individuals to extract sensitive information through seemingly legitimate emails. These attacks can lead to serious data breaches and financial theft. With a 61% increase in reported phishing attacks, it is vital to stay ahead of email and phone phishing attacks.
Callback Phishing
A new twist in phishing tactics is ‘callback phishing,’
Highlighted in a recent FBI warning. In this method, victims are tricked into calling a fraudulent phone number, leading to potential malware installation or data breaches. This evolution in phishing highlights the importance of adapting security strategies to emerging threats.
Ransomware
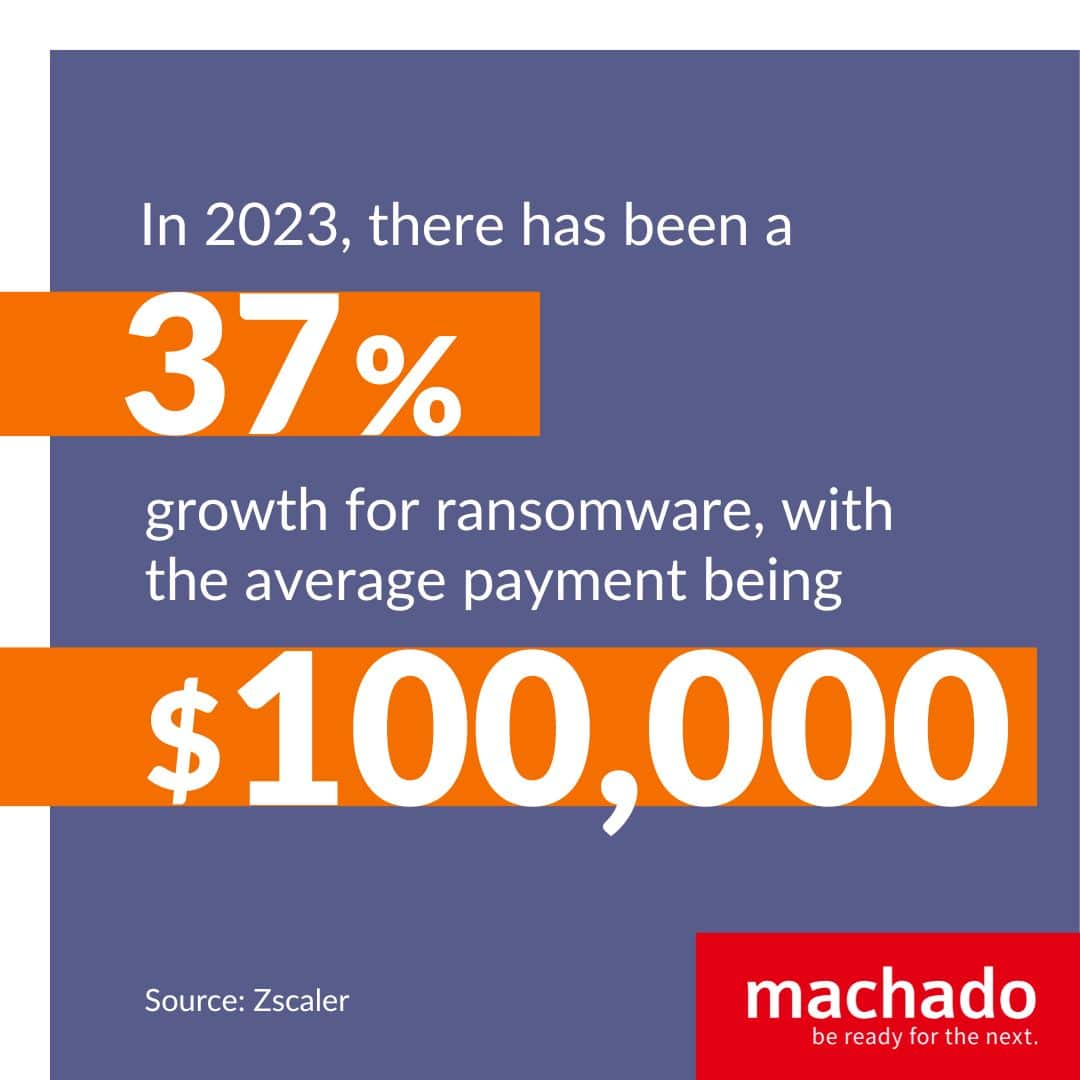
Ransomware remains a significant threat, with attacks escalating in both frequency and severity. These malicious software attacks lock your businesses out of systems, often resulting in operational downtime and financial losses, with the average payment of ransomware attacks exceeding $100,000 in 2023, and on the rise with reported cases growing by 37% in 2023.
DDoS Attacks (Distributed Denial of Service)
DDoS attacks aim to overload networks with excessive traffic, causing service interruptions and damaging business operations and reputation.
With nearly 8 million reported DDoS attacks last year, preparing for these attacks is crucial.
Preventing these attacks requires network security management to ensure uninterrupted service and protect customer trust.
These threats translate into real-world challenges, from operational disruptions to financial strains.
Understand the importance of implementing effective network security monitoring to safeguard your business.
The Real-world Impact on Businesses
The repercussions of cyberattacks extend beyond immediate technical challenges.
They affect the entire spectrum of your business operations.
They not only disrupt day-to-day activities but also carry substantial financial and reputational costs.
This section aims to unpack these real-world impacts, demonstrating the often-overlooked consequences of cyber threats and reinforcing the importance of effective network security monitoring.
Operational Downtime
Cyberattacks, particularly those like ransomware or DDoS, can halt business operations.
This downtime not only results in lost productivity but also in lost revenue and potential customer dissatisfaction.
Financial Repercussions
Beyond the immediate expenses like ransom payments, businesses often incur costs in system repairs, data recovery, and increased security measures. There’s also the potential for lost business and legal ramifications in the wake of a breach.
Reputation Damage
Your company’s reputation is invaluable. Securing your server is key to securing your company’s reputation.
A single significant breach can erode customer trust, leading to a loss of clients and difficulty in acquiring new ones.
The long-term impact of reputation damage can be one of the most challenging consequences to mitigate.
With a clear understanding of the extensive impacts of cyberattacks on your business, we now turn to the solutions.
Proactive Managed Service Providers explore the various strategies to not only counteract the threats we’ve discussed but also to fortify your business’s digital presence in the future.
How MSPs Improve Cybersecurity
Managed Service Providers (MSPs) fight against digital security breaches by providing a range of solutions and services designed to fortify a company’s cybersecurity infrastructure.
Proactive Monitoring
Proactive monitoring is at the heart of what Machado offers.
By constantly overseeing your network, MSPs can detect and address potential threats before they escalate into major issues. This continuous vigilance is key in preventing attacks and minimizing their impact.
Regular Updates and Patches
Keeping systems up-to-date is crucial for security. MSPs ensure that all software and systems are patched with the latest updates, closing vulnerabilities that could be exploited by cybercriminals.
Backup and Disaster Recovery
A comprehensive backup and disaster recovery plan is a must-have in today’s digital world. Machado can provide regular backups and efficient recovery solutions to protect against data loss in the event of a cyberattack.
Employee Training
Human error is a significant factor in many cybersecurity breaches. MSPs often offer training programs for employees, educating them on best practices and how to recognize potential threats, which is vital for maintaining a secure digital environment.
Custom Security Protocols
Every business has unique security needs. MSPs tailor their security protocols to fit the specific requirements of your business, ensuring a personalized and effective defense strategy.
Your business can navigate the complexities of cybersecurity with greater confidence, ensuring both the safety of your digital assets and the continuity of your operations.
The Tangible Benefits of Partnering with an MSP
The decision to partner with a Managed Service Provider (MSP) extends beyond just cybersecurity. It brings a spectrum of tangible benefits, crucial for your business.
Peace of Mind
One of the foremost advantages of collaborating with an MSP is the peace of mind it offers. Knowing that your network security is continuously monitored by a team whose core value is to protect your business allows you to focus on core business activities without the constant worry of cyber threats.
Cost Efficiency
Proactively managing cybersecurity with an MSP can be more cost-effective in the long run. By preventing breaches and minimizing downtime, MSPs help avoid the hefty costs associated with cyber incidents. This foresight in security planning can lead to significant financial savings.
Operational Continuity
Ensuring operational continuity is a critical aspect of MSP services. With their expertise, MSPs implement strategies that minimize disruptions, maintain service availability, and ensure that your business operations run smoothly, even in the face of digital threats.
Partnering with an MSP not only strengthens your cybersecurity but also contributes to the overall resilience and efficiency of your business operations.
With a deeper understanding of cyber threats and the value MSPs bring in addressing them, you can visualize the benefits network security monitoring provided by a Proactive MSP like Machado.
Monitoring Your Network Security with Confidence
In this comprehensive overview, we’ve addressed the multifaceted nature of cyber threats that your business may face today, from phishing and callback phishing to ransomware and DDoS attacks. Each presents unique challenges, underscoring the need for vigilant network security monitoring. The role of Managed Service Providers (MSPs) is invaluable, offering proactive solutions that create network security monitoring that stops issues before they occur.
The real-world impacts of cyberattacks – operational downtime, financial losses, and reputational damage – highlight the critical importance of effective cybersecurity strategies. MSPs provide peace of mind, cost efficiency, and operational continuity, proving to be indispensable partners in safeguarding digital assets.
The importance of network security management cannot be overstated. This is why partnering with Proactive Managed Service Providers, like Machado, can save your business from harmful cyberattacks, and create top notch network security management and monitoring.
Download our guide to learn how you can get more done with your current IT staff.Be Ready for the Next IT Opportunity