When it comes to your computers and personal devices, whether in the workplace or at home, you’re probably either on Team Mac or Team PC. If you’re on Team Mac, you probably tout the security of your devices.
You feel safer, less vulnerable to cybersecurity threats. After all, how often do you hear about an Apple security alert compared to the threats for PCs? The idea that Apple devices are safe from hackers is actually a misconception. If you use Apple devices, you, too, are vulnerable to cybersecurity threats.
Cybercrime is big business and in 2021 the costs are estimated to be $6 trillion, making the cybercrime industry the third-largest economy in the world. Like any business, cybercrime allocates resources according to the best return on investment (ROI). If bad actors can develop a virus in 40 hours that will infect thousands, if not millions, of computers with a Windows operating system, why would they spend time on a virus to infect less than 10% of the computer market? 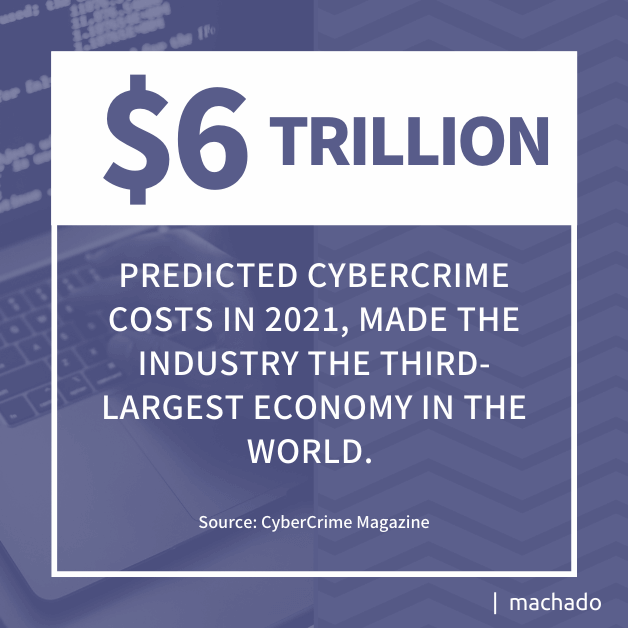
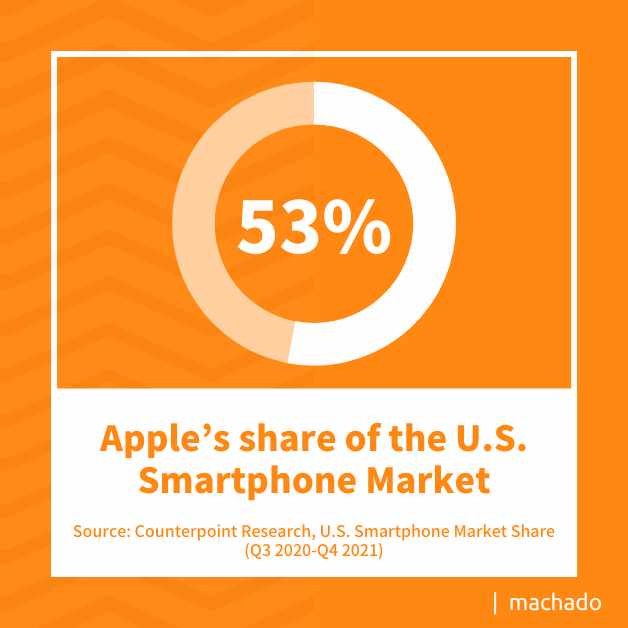
Changes in the work environment, as well as the continued increase in smartphone usage, mean people need to become aware of the security vulnerabilities of Apple products. Whether it is malware or mobile viruses, Apple products are as susceptible to cyber attacks as any other internet-connected device. When it comes to awareness of Apple security alerts, here are the five threat categories you should watch closely:
1. Malware
Hackers are developing malware that no longer depends on an operating system. Instead of looking at the OS, developers are focusing on plug-ins that operate above the OS layer, making it possible to build one application that works on every computer in the world. In the same manner, hackers are developing malicious code that operates cross-platform, generating an even better return on their time investment. 
- ElectroRAT. A cross-platform remote access trojan (RAT) that targets cryptocurrency that is delivered through an application trojan that can take screenshots, execute commands, and log keystrokes as well as uploading and downloading files.
- SilverSparrow. A virus targeting the M1 chip of MacOS devices in about 30,000 instances.
- XcodeSpy. A form of spyware designed for software developers as it is delivered by malicious Xcode projects.
- ElectrumStealer. Malicious code that leverages Electrum wallet to steal cryptocurrencies through a backdoor.
- WildPressure. Windows malware that’s made its way into Apple’s operating systems.
- XLoader. A cross-platform malware that steals passwords.
- ZuRu. Malware that targets China’s search engine Baidu to deliver a bogus iTerm site that downloads adware when accessed.
- CDDS (MacMa). Malware that exploits a zero-day vulnerability to capture keystrokes, fingerprint compromised devices, record audio, and manipulate files.
The primary objective of most Apple malware may continue to be adware, but with more focus on Apple products, cyber criminals will extend their reach. For now, the best way to protect against infection is to install Apple updates promptly.
2. Internet of Things (IoT) Security Threats
As more people use Apple Watches and AirTags, cybercriminals will continue to leverage vulnerabilities to deliver malicious code or to pursue physical-world crime. AirTags have come under special scrutiny in recent months because of their stalking capabilities.
AirTags
For example, a female left a bar on a Friday night. As she drove away, she received alerts saying an AirTag was moving with her and that it was visible to the owner. Panicked, she checked her coat, wallet, purse, and other items, but could not find the AirTag. Because she was afraid of being stalked, she did not go home. In the morning, she had someone check her car where they found the AirTag in her wheel well. Several states have recently issued warnings regarding the illegal use of AirTags.
Being able to track individuals without their knowledge opens the door to crimes such as home invasions, stalking, and burglary. Once criminals know where a potential victim lives, they can capitalize on the information in ways that go beyond the virtual world. Learning how to disable unwanted tracking is the best way to ensure one’s personal safety.
AirTags have been used in drop attacks. In drop attacks, cybercriminals drop compromised USB drives in public locations, hoping that someone will pick them up and use them. When inserted into a USB port, the software is transferred to the device and the hacker has access to the device and anything connected to it.
With AirTags, bad actors enter cross-scripting executables (XSS) into the phone number field to capture end-user credentials after a device is scanned. When the device is set to ‘Lost’, someone should be able to scan the tag and have a window display at found.apple.com without compromise. Instead, hackers direct users to a malicious website where the information in the phone field is recorded. Apple has yet to provide a comprehensive fix for AirTag or Apple Watch zero-day vulnerabilities.
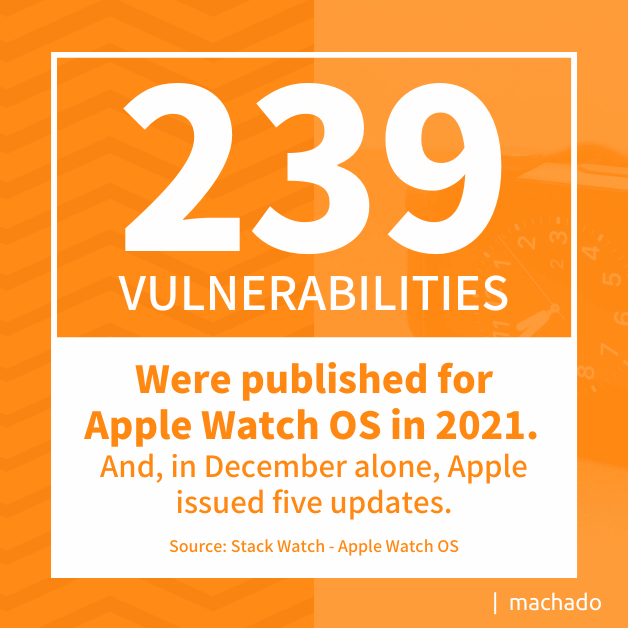
Apple Watch
Apple Watch OS had 239 vulnerabilities published in 2021. In December alone, Apple issued five updates:
- CVE-2017-13905. Security update to prevent applications from gaining elevated privileges.
- CVE-2017-13880. Security update to address memory corruption issues to stop applications from executing arbitrary code.
- CVE-2018-4302. Security update to prevent malicious XML from terminating an application or executing arbitrary code.
- CVE-2021-30767. Security update to prevent local users from modifying the protected file system.
- CVE-2019-8703. Security update to prevent applications from gaining elevated privileges.
All but one of these updates were considered critical or high priority. Watch users need to apply the latest updates to protect against possible infection.
3. Mobile Threats
In late 2021, Apple released an emergency update for its iOS when it was notified of a vulnerability that the Pegasus spyware exploited. Pegasus, developed by Israel’s NSO Group, is invasive spyware that can monitor individuals without their knowledge. It is used by governments, criminals, and private citizens to capture information by:
- Turning on cameras and microphones
- Recording messages, texts, and emails
- Decrypting encrypted messages
Although Pegasus was first detected on Apple’s mobile devices, it has since been found on Apple Watch and macOS. The iOS update 14.8 contains the patch for the spyware vulnerability on mobile devices. Release 11.6 addresses the Pegasus vulnerability on Mac. Additional security flaws have been identified since Pegasus and security patches have been released to address these issues. Release 15.3.1 of iOS and iPadOS are the most current updates for mobile devices.
4. Browser Security Flaws
Recent security vulnerabilities have been identified on Safari 15 and Chrome running on Apple operating systems. Both flaws represent significant threats to individual users. Although updates are available, they may not be released in all environments. If your browser is still at risk, switch to a different, but protected, solution until an update is available.
Safari 15
Safari 15 contains a vulnerability that allows hackers to track browser activity across multiple websites and to reveal user identities. Web browsers use IndexedDB to store client data and to prevent unauthorized access based on the same-origin policy. When a user accesses a website, their data is recorded with the originating request information identified. If subsequent interactions come from a different originating address, the activity would be disallowed.
Apple’s Safari 15 on macOS and browsers running on iOS and iPadOS 15 devices violate this same-origin policy. When a website interacts with the Indexed DB API, an empty database with the same name is created for all other active windows, tabs, or frames accessed during the same browser session. As a result, arbitrary websites can see what occurs on other active websites.
For sites such as Google Calendar, YouTube, and Google Keep, authenticated users are identified in such a way that the personal information in your Google ID could be leaked. With access to that personal information, hackers are free to create havoc with personal data.
Chrome
Google’s latest zero-day vulnerability has been exploited in the wild according to Google. In total, Google is addressing seven high-level cybersecurity threats in Chrome that impact every operating system. Specific information is being restricted, so details are lacking.
What is known is that the majority of the hacks use a use-after-free (UAF) exploit where the memory pointer is not cleared after the memory is released. A secondary hack takes advantage of a buffer overflow that enables critical data structures to be overwritten. Chrome 98.0.4758.102 contains updates that address the latest vulnerabilities.
In some instances, the update may require a manual intervention to install. To check if your browser is protected, go to Settings>Help>About Google Chrome to see if the release is 98.0.4758.102 or higher. If not, consider using an alternative until one is available.
5. Using Personal Devices at Work
Users of Apple products are conditioned to believe their iPhones, iPads, and Macs are not susceptible to cybersecurity threats. But, that is an Apple security myth. Apple users are just as likely to receive a MacOS security alert as a Windows one. The difficulty is that few Apple users are looking for those alerts. 
You can request a free network security audit here.
While Mac laptops and desktops may have fewer cybersecurity threats, they are not immune to cyber attacks. As their usage continues to grow, they most likely will become more frequent targets, so right now is the time for you to pay attention to ongoing threats.