If you’re like most people today, you’re suffering from information overload. Our news sources are varied — internet, TV, social media, and streaming services. With so much incoming data, it’s hard to know what to consume and what to ignore. Cybersecurity hacks in 2022 haven’t always made it “above the fold,” but that doesn’t mean they aren’t happening. Some of the best lessons in cybersecurity prevention come from the lapses in security faced by other organizations around the globe. Here’s a roundup of seven security compromises during the first half of this year and the lessons you can learn from their mistakes to help you better protect your business.
Crypto.com
Yes, cryptocurrency companies use blockchain for more secure transactions, but the technology is not always used for identification. In January 2022, Crypto.com experienced a breach of 483 accounts. Hackers were able to circumvent the company’s two-factor authentication to steal about $35 million (US). The funds were primarily in Ethereum or Bitcoin. Less than $75,000 (US) was in other currencies. Initially, the company reported that no funds were stolen. Later they indicated that no customers suffered losses. If funds were illegally withdrawn, customers were reimbursed. Days before the company detected unauthorized activity on user accounts, customers had complained that funds were missing from their accounts. When crypto.com discovered the breach in late January, they halted all withdrawals and hardened security measures. As a result, the service was down for about 14 hours. According to the company, they’ve implemented a white-listing of withdrawal addresses. This means the address must be registered — put on the white-list — at least 24 hours prior to the first withdrawal. If someone attempts a withdrawal, the requesting address is checked against those on the whitelist. If the address is not present, the transaction is denied. Customers will receive alerts to help manage their accounts. Crypto.com will also move to multi-factor authentication (MFA) instead of its current two-factor authentication (2FA). 
Chinese Police Database
Chinese authorities amass vast amounts of data on their citizens. They track movements, stalk social media, and keep DNA records. When a breach is successful, cybercriminals gain a wealth of information. In July, news was shared that the Shanghai Police Department’s server was hacked. A best-guess estimate is that information on over a billion people was stolen. An anonymous user posted in an online forum that information from the Shanghai database was for sale. Another anonymous user offered to sell a police database from Henan province with information on 90 million individuals shortly after the Shanghai breach was disclosed. Apparently, the servers were unsecured. Of course, the Chinese government has made no comment as the breaches do not portray their cyber defenses in a positive light. More importantly, the government has blocked all news regarding the breach from appearing on Chinese internet and media platforms. Many Chinese citizens are unaware the breach occurred. The government is trying to contain news of the breach, fearing a possible confrontation. At the same time, more citizens are voicing concerns over data privacy. Lesson: Businesses must ensure that their servers are secured. Securing the perimeter is not enough to protect your valuable digital assets.
Red Cross
The International Committee of the Red Cross (ICRC) reported a server compromise in January 2022, although it appears the intrusion began as early as late November 2021. The cybercriminals stole data on families the agency was trying to unite. At the time of the discovery, the Red Cross asked the hackers to keep the data confidential because the information pertained to vulnerable families around the globe, torn apart by conflict or natural disasters. 
Cash App
Cash App is an internal application that Block — formerly Square — uses to download financial reports. The reports can contain names, account numbers, and portfolio values. News of the breach hit the media in April 2022. It shared that in December 2021, an ex-employee was able to access Cash App and download a series of reports.The number of compromised accounts has not been released, although the company has contacted over 8 million existing and former customers. The unauthorized access made news after it was reported to the Securities and Exchange Commission (SEC) on April 4, almost four months after the unauthorized download of information.The company has not released additional information beyond its initial filing with the SEC. However, Block stated that no customers outside the United States were impacted. It is not publicly known when the employee who accessed the reports left the company or why their credentials were not blocked, deleted, or deactivated. Block is working with all regulatory agencies and has launched an internal investigation. Lesson: Every business should have procedures in place to ensure that all access is blocked when an employee leaves the company.
Microsoft
Microsoft is often a target for cybercriminals. The latest attempt was by Lapsus$.– a relatively new group that is not shy about publicizing its exploits. The group is believed to be located in South America and uses the following tactics to compromise network security:
- Use Redline password stealer
- Buy credentials from Dark Web forums
- Pay a target’s employees for credentials
- Search public code repositories for possible credentials
When the group breached Microsoft’s defenses in March 2022, they were quick to report the compromise. Microsoft indicated that Lapsus$ had compromised an employee’s account to gain limited access to some of its source code repositories. Microsoft has repeatedly indicated that it “does not rely on the secrecy of code as a security measure and viewing source code does not lead to elevation of risk.” While the company’s security center is investigating the event, Microsoft stated that no customer information was compromised. 
Nvidia
In February 2022, Nvidia experienced a network security breach that resulted in hackers stealing sensitive data including employee credentials and proprietary information. Like the Microsoft attack, Lapsus$ claimed responsibility and threatened to release the stolen information unless these demands were made. They wanted Nvidia to:
- Provide open source code for their GPU drivers.
- Disables LHR.
- Pay an undisclosed amount.
Nvidia recently made changes to their graphic card drivers (LHR) to restrict their performance to limit cryptocurrency mining. Nvidia’s dominance in the graphics card market also made them a target for turning their proprietary code into open source. In response to the demands, Nvidia launched a ransomware attack against Lapsus$ to prevent the release of stolen information, according to the cybercrime group. Nvidia has not responded to the accusation. The cyberwar between Nvidia and Lapsus$ has yet to be resolved, and neither side is talking. The Lapsus$ group released source code related to Nvidia’s proprietary DLSS technology as well as information on 71,000 employees. Nvidia has not released its GPU source code or removed the LHR feature from its products. Lesson: Ransoms are not always about money.
Bridgestone
On February 27, 2022, Bridgestone learned of a potential cyberattack. To minimize the impact, the company disconnected manufacturing and retreading facilities in the Americas and workers were sent home. It took 10 days before the manufacturing facilities in North and South America were re-opened. The company is working with regulatory agencies and has hired Accenture Security to help with the forensics surrounding the breach. LockBit 2.0 claimed responsibility for the ransomware attack and threatened to go public with the stolen information if the ransom was not paid. LockBit 2.0 is a cybercrime gang made up of individuals who outsource their skills, as well as use them to extort large tens of millions of dollars for return of the stolen data. The attack uses a self-spreading malware that leverages tools such as Windows Server Message Block and Powershell. The FBI issued an 11-page document on LockBit 2.0 in early February because of its dominance in the last half of 2021. Lesson: Businesses must stay informed on cybersecurity threats.
7 Lessons Learned to Better Protect Your Business
The above real world examples of cybersecurity breaches over the past few months are eye-opening. The take-away from these stories is that you should always be learning from the security failures of other organizations. Here’s a wrap up of the learnings from the stories you just read:
1. Deploy Stronger Authentication
Stronger authentication is the first network security protection to put in place. With more employees working remotely or in a hybrid environment, it’s important to have an authentication method that minimizes the risk of stolen credentials. As Cyrpto.com learned, authentication is only as good as its implementation.
2. Secure You Network
As more networks become distributed, every device must be secured. Protecting the perimeter is no longer sufficient when it can change overnight.Knowing the devices that are connecting to your network is equally important, especially if you allow employees to bring their own devices. Many security experts suggest being proactive and moving towards a zero-trust architecture to strengthen your security posture.
3. Every Company is a Target
No matter the size of your business, it is a potential target. Your business may be a step in a supply chain attack. You may be collateral damage if a software update contains a virus. You may not be the target of an attack like the Red Cross, but you can still fall victim to cybercrime.
4. Look for Insider Threats
Make sure you deactivate users the minute they no longer work for your business and limit user activity using a least-privilege model. Employees should be given access to resources they need for their job, but not to the entire network.
5. Know the Cybersecurity Landscape
New cybersecurity threats appear almost daily which is why businesses need to stay informed. Knowing how a gang such as LockBit operates can help identify a potential attack before it can compromise your system. Monitoring CISA or FBI websites can help keep you current on the evolving landscape.
6. Ransoms Are Not Always Money
Recent extortion attempts from Lapsus$ indicate a change in the hacker’s mindset. Ransomware attacks have always been about money; however, ransom demands could expand to include shutting down factories or increasing wages.Consider your options before the demand is made.
7. Train Your Staff
Every employee needs to be trained on how to detect and respond to a possible cybersecurity threat. The more people know about and understand cybersecurity threat prevention techniques, the better they can protect against a misstep. 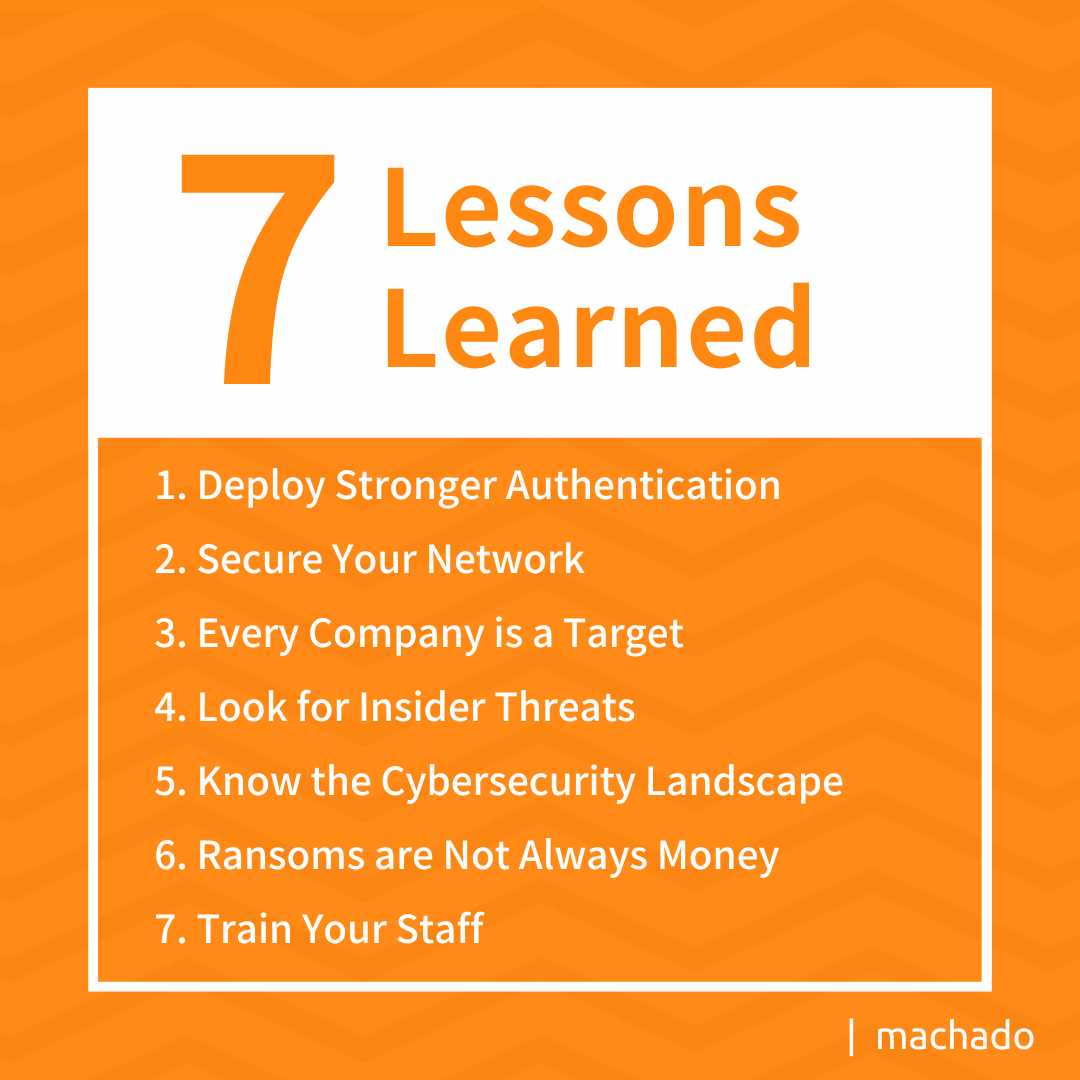
Need Help?
If reading about these 2022 cybersecurity hacks have you concerned about your own business, you may want to consider working with a co-managed IT partner. Let’s talk about how we can help you to develop a comprehensive plan to protect your digital assets. Let’s work together to make sure that the only lessons to be learned from your business when it comes to cybersecurity are how to avoid the threats others may miss.